Not only does the credit bureau max out their password length, you have a small list of available non-alphanumeric characters you can use, and no spaces. Also you cannot used a plused email address, and it had an issue with my self hosted email alias, forcing me to use my gmail address.
Both Experian and transunion had no password length limitations, nor did they require my username be my email address.
Update: I have been unable to log into my account for the last 3 days now. Every time I try I get a page saying to call customer service. After a total of 2 hours on hold I finally found the issue, you cannot connect to Equifax using a VPN. In addition there is no option for 2FA (not even email or sms) and they will hang up on you if you push the issue of their security being lax. Their reasoning for lax security and no vpn usage is “well all of our other customers are okay with this”.
Yeah well, if you’re so smart let’s see you write a website in COBOL.
no spaces in a string is a dead giveaway that theres Cobol in there somewhere meow
meow
?
their name is kittykittycatboys what else do you expect :3 meow
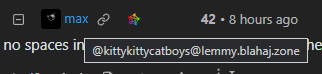
It shows up on my screen as merely “max”, nothing else.
Username and display name can be set independently, you should have a “Display name” field in settings. Their non-unique display name is “max” and their unique username is “@kittykittycatboys@lemmy.blahaj.zone”. If you check their profile you should see both.
If you don’t set a display name it will be the same as your username, if you set display name to the same as username (like I have) it’ll show your username without the instance even to people on other instances.
Oh, I see. Thanks.
If you open the profile it seems to have two names. I have the feeling that only one of them is valid with the instance postfix, despite it being shown with both
Where would max even come from? That’s not in their username o.O
Max is the name of the cat, duh.
Mew!
Meow do you like to drink milk from a saucer?
You joke, but…
- https://www.microfocus.com/documentation/visual-cobol/vc70/VS2017/GUID-78091B18-A9B3-4212-BE5F-3E28C7196413.html
- https://github.com/loveOSS/awesome-cobol
(No, I will never forgive the college I went to for undergrad for forcing us to take two semesters of COBOL. Why do you ask?)
I actually clicked on all the web-related Awesome Cobol links yesterday. Each one is either a broken link or golang code.
“We serve
foodsanity here, sir”
This implies they’re storing the plaintext password.
Ideally the password would be hashed with a salt and then stored. Then it’s a fixed length field and it shouldn’t matter how long the password is.
Or a very very old database system, possibly DB2, where you can’t change the column limits or data types after the fact.
If they’re hashing, the column size should be irrelevant. Ideally the database should never see the plaintext password in the first place (though I could understand calculating the hash in the query itself). If they’re not hashing, they should really be rewriting their database anyway.
Salted passwords are not recommended anymore. Better to use a memory hard key derivation function designed for passwords, like Argon.
Those are salted, they just do it for you.
Where does the salt get stored?
It’s usually part of the string stored to the DB.
Edit: you can see the PHC spec here:
https://github.com/P-H-C/phc-string-format/blob/master/phc-sf-spec.md
Which is a common format for various password storage algorithms, including Argon2. It has a salt field.
I’d rather see a paper explaining the flaws with salted passwords rather than “just use this instead”.
My initial reaction is that this overcomplicates things for the majority of use-cases, and has way more to configure correctly compared to something basic like a salted sha256/sha512 hash that you can write in any language’s standard library.
If the database of everyone’s salted password hashes gets leaked, this still gives everyone plenty of time to change passwords before anything has a chance of cracking them. (Unless you’re about to drop some news on me about long time standard practices being fundamentally flawed)
Wut. Is the competition not enough data for you? This is how we got AES.
Can you name a single popular language where Argon2 isn’t implemented in a stamdard library?
I think you’re missing the point of what I’m asking. In what way are regular salted passwords insecure? Sure you can keep adding extra steps to encryption, but at a certain point you’re just wasting CPU cycles.
I have no doubts about Argon2 being secure, I just think the extra steps are unnecessary for anything I would build (i.e. not touching financial transactions or people’s SSNs). By design argon2 uses a lot of memory and CPU time to make bruteforce attacks much harder, but that’s more of a downside when you’re just doing basic account logins on a low end server.
I’ll happily retract my point about external dependencies. It’s available in most languages, and notably std C++ contains neither argon2 or sha256/512 hashing, so that kind of makes my original point invalid anyway.
Credit bureaus are not for your protection, they’re for the protection of their clients, the banks.
Banks aren’t much better. Up until just a couple years ago, the Treasury Direct website (to buy bonds/etc from the US Treasury) forced you to use a god damned on-screen keyboard to input your password and the passwords were not case sensitive. I’m pretty sure it also only read the first X number of characters of your input because I recall that people tried typing extra characters after their passwords and it would still accept it as valid, though I could be conflating this with some other archaic site.
You are unable to paste your password into the “confirm password” field. I thought I was going to have to type it in, but Bitwarden’s autofill worked.
The first part I’m sure about because I had to create a bookmark of a line of javascript that would bypass the on-screen keyboard and allow you to autofill the password. It was sometime in the last 3 or 4 years that they finally joined the 1990s and updated it
Financial institution security is quite frankly a freaking joke. My bank only has the options for 11 character passwords at maximum. It’s like oh come on that is way too easy these days
Removed by mod
Honestly, that’s a sign to me that your bank doesn’t take cybersecurity seriously and would possibly consider switching. Mine has amazing security as well as fraud detection. Sometimes it’ll even send me a text to verify a purchase if their software thinks it’s weird I got across town too quickly, though that’s pretty rare so it isn’t overly aggressive/inconvenient.
In Germany at least, I hear that banks have weird law requirements for these weird security things, like photoTAN.
I’d be much happier if they’d just let me do my usual setup with password, totp and my hardware token.
In the US the FDIC sets security requirements for banks and audits annually, and they keeps raising requirements every year or so. At this point its just easier for a bank to invest in following current best practices and keep updating to the current best practices than to keep chasing every new finding on the FDIC audits each year
Source: I worked in IT at a bank for a while
A 20 character password of case insensitive letters and numbers is quite unbreakable (taking billions of years to brute force). Still, what a strange way to announce your database is old and you probably aren’t hashing your password with anything stronger than MD5. Or worse.
My default is to generate a 32 character password and store it in a password manager. Doesn’t matter to me how many characters it has since I’m just going to copy and paste it anyway.
Pretty surprising how many places enforce shorter passwords though… I had a bank that had a maximum character limit of 12. I don’t bank with them anymore. Short password limits is definitely is an indicator of bad underlying security practices.
A hash has a fixed length, including MD5. There’s no reason to cap password (input) Iength. You can hash the whole bible and still get the same length hash. So either they don’t even hash it, they’re idiots, or they try to be unnecessarily cautious to avoid some other limit / overflow, like POST max size (which would still be counted in at least KB, not several characters). The limit on what special characters you can use is also highly suspicious - that’s not how you deal with injections / escaping your inputs.
Hashing takes longer the longer the string is, so it technically could impact performance if many people with very long passwords log in simultaneously. 20 characters is ridiculous though, you could probably cap it at hundreds and still be completely fine.
the Ring app (I think) forced me to change my Wi-Fi password because I wasn’t allowed to use ampersands. according to support it’s because they “use ampersands in the code”
You mean the company that had a feature in place that allowed law enforcement to request and access video footage from your devices without obtaining a warrant first?
As expected, their security measures were also found to be lacking.
Yeah, no thanks.
It deeply saddens me when people pay money for locked down hardware that’s not only designed to spy on them, but their family, friends, and neighbors as well. Ring, Amazon Echo, Google Home, that creepy Facebook robot screen…all insecure spyware.
yeah I only have a ring for my outdoor cameras. I was considering switching my indoor system yo ring as my alarm company keeps raising their prices but I’m not putting ring cameras inside my house. especially because the privacy shutters on them are manual
Thats the least of your worries with Ring. Put that shit straight into the bin.
Sure would be a shame of Bobby tables made a ring acct
The problem is quotes, not spaces and ampersands
Then wash the code! Son’s of bitches!
That implies that they pass parameters in URLs… FFS.
Eufy cameras will not allow spaces in the WiFi password.
I encountered something like this at work. It wasn’t pass related, it was just a means of getting people to make text responses. Ampersands were replaced with some gibberish format, which annoyed everyone.
I got some kind of explanation from our tech people, which I understood to mean that ampersand was used to indicate that what followed was live code. Turning the ampersand into gibberish text was a safety measure to stop mischief.
I’ve noticed ampersand replacements in some news feeds too
Literally this
Except todays wordle answer cannot be made to multiply to 35
I got to rule #16 - I suck at chess. Secret to “multiply roman numerals” is just add them up to the value.
Rule 5 The digits in your password must add up to 25.
Imagine having to contract with a company in order for them not to fuck your life up with your own data. This is ridiculous.
that they collect without your explicit consent
You signed a contract? Pretty sure they’re going to fuck it up either way and they definitely have all your data.
My bank used to not let me type one longer than six (6) characters!
My bank disables paste as has code checking if the browser is greater than Netscape Navigator 4.
Goddamn I really hate that shit.
https://addons.mozilla.org/en-US/firefox/addon/don-t-fuck-with-paste/
I wrote a TamperMonkey script. 😅 I needed to so I could use my password manager. How dare I.
Should be a general web dev usability note: always aim to make your code to be friendly for scraping & userStyles/userScripts. If a client isn’t updating shit, at least users can easily fix things. This is also another point against this Tailwind-only trend since you tend to lose anything semantic in the DOM & have nothing to select on.
Removed by mod
Yup. My bank was even “translating” passwords to PINs behind the scene specifically so your password for the website would be the same as your password on the telephone.
I also like that the only type of MFA that all 3 agencies implement is text/phone call. Cause likes there’s nonway someone could spoof a phone number and then unfreeze your credit.
Financial companies ans banks and stuff have to follow regulations on their MFA method. That why you can’t just use any OTP authenticator and are stuck with email/SMS.
In case anybody’s curious about what those are:
- https://rublon.com/blog/nydfs-23-nycrr-part-500-mfa-compliance/
- https://metomic.io/resource-centre/financial-services-compliance-regulations
- https://rublon.com/blog/ffiec-mfa-compliance-best-practices/
- https://www.ffiec.gov/press/pdf/Authentication-and-Access-to-Financial-Institution-Services-and-Systems.pdf
The biggest reason they use phone calls or SMS, however, is because they don’t want to go to the hassle of getting an in-house MFA service (a TOTP backend, in other words), approved, pen tested, analyzed, verified… all things considered, it’s faster and easier to go with a service like Twilio that already did all that legwork. A couple of years back I worked for a company in just that position, and after we did all the legwork, research, and consultation with the independent third party specialists trying to run our own TOTP would have easily doubled the yearly cost because of all the compliance stuff.
Adding TOTP would be cheaper in the long run than continuing to pay those SMS rates. I dont think its about any kind of extra hassle they have to deal with. More of terrible NIST standards written by the center for internet security, which is a for profit corporation that apparently nist allows to write all their standards
It really depends on the company. When I was working for that company a few jobs back, we crunched the numbers and the cost of C&C and IV&V (Certification and Accreditation; Independent Verification and Validation) for an in-house TOTP had one more zero to the left of the decimal point than the Twilio bill (added up for the year). Plus, for compliance we’d have to get everything re-vetted yearly.
That’s kinda of the definition of government contracting. :) I think the only US government org that has actual govvies doing anything other than management is NASA.
Yeah except you only have to spend the money once as opposed to paying twilio every year
for compliance we’d have to get everything re-vetted yearly
Removed by mod
And I use password manager, I don’t care of its 52 chars long, I just use the software to fill the field
Removed by mod
I recommend Diceware for generating memorable passwords of sufficient complexity…but also, a password manager.
I use a 5 word phrase generated by my password locker. I will add a symbol or three to it if required.
that is a painfully bad list of
requirementsbullshitshort passwords because they are trying to save bandwidth for their next time their entire database structure is downloaded
They’re supposed to be hashed so that shouldn’t matter
Unless that’s the joke or something
That’s security theater for you…
I have seen this on a site before and I never understood why. Whats the point of limiting the length of the password? Its not to save storage space since the plain text isnt stored and the hash should be a uniform length. So whats the advantage?
since the plain text isnt stored
I’m not sure I’d accept a bet on that assumption.
deleted by creator
Calculating hashes is supposedly more expensive for longer strings. That could be used to simplify some kind of overload attack like DDOS.
If they’re not already rate-limiting login attempts that’s another huge problem…
If they’re using md5 (which would be in line with their security practices), the block size is 512 bits. That means that everything less than 64 characters is the same cost